Context is everything
When most people think of penetration testing, they picture a fairly standard process: scan the application, flag vulnerabilities, assign a severity score, and ship a report.
It’s neat. It’s structured. It looks good in an audit.
But here’s the problem: attackers don’t think that way.
They don’t care about a severity score in isolation. They care about how different flaws in your environment can be chained together, abused in your workflows, and leveraged against your users.
And that’s where many pentests fall short. They miss the context.
Why generic pentesting isn’t enough
Let’s break down why a one-size-fits-all pentest can leave major blind spots:
Business logic risks are overlooked
Traditional scanners and checklists are great at spotting technical issues like SQL injections or open ports. But they rarely catch business logic flaws. The subtle gaps in how features behave when pushed outside normal use are never paid attention to.
Severity doesn’t always match real-world risk
Many reports use CVSS scores as the north star. But a “Medium” vulnerability in an authentication flow could be far more damaging than a “High” in a low-privilege API endpoint. Without context, teams often waste time fixing the wrong things.
Tech stack differences matter
A microservices-based SaaS with GraphQL APIs has different risks than a legacy PHP monolith. Yet many pentests run the same set of canned tests across both. That’s like securing a bank vault and a coffee shop with the same lock.
Compliance ≠ security
Passing PCI-DSS, SOC2, or ISO audits doesn’t guarantee safety. Compliance ensures you’ve met a baseline, but attackers exploit gaps outside those baselines. A report that focuses only on compliance misses the bigger picture.
How context makes pentesting stronger
If attackers think in terms of context, defenders should too. How exactly do we do this?
1. Business-centric threat modeling
Instead of starting with a checklist, testers should start with questions:
What’s the most valuable data in this app?
Who would want it and why?
What workflows, if abused, could cause financial or reputational damage?
This lens changes everything. For instance:
A fintech app’s refund workflow is a goldmine for fraud.
A healthcare app’s file upload function is a potential privacy nightmare.
A SaaS app’s invitation link system could be abused for privilege escalation.
When pentesters know your crown jewels, they can focus efforts where it matters most.
2. Attack chain thinking
Real attackers rarely rely on a single bug. They chain smaller issues to create a breach. Context-aware testing simulates this.
Weak authentication → exposed API → lateral movement → sensitive data leak.
Individually, each issue might look minor. In context, it’s a disaster.
3. Impact-driven prioritization
Not all vulnerabilities deserve the same attention.
Example: A “Medium” issue that allows brute-force attempts on an admin login page is far more urgent than a “High” reflected XSS in a low-traffic marketing subdomain.
Context turns raw findings into actionable priorities.
4. Environment-specific testing
The same vulnerability can look very different across environments:
A misconfigured S3 bucket storing test data = nuisance.
A misconfigured S3 bucket storing production PII = regulatory nightmare.
Context ensures tests reflect what’s truly at stake.
Beagle Security’s approach
At Beagle Security, we’ve built AI-driven automated pentesting that adapts to each application instead of forcing everything into a template. Here’s how we put context at the core:
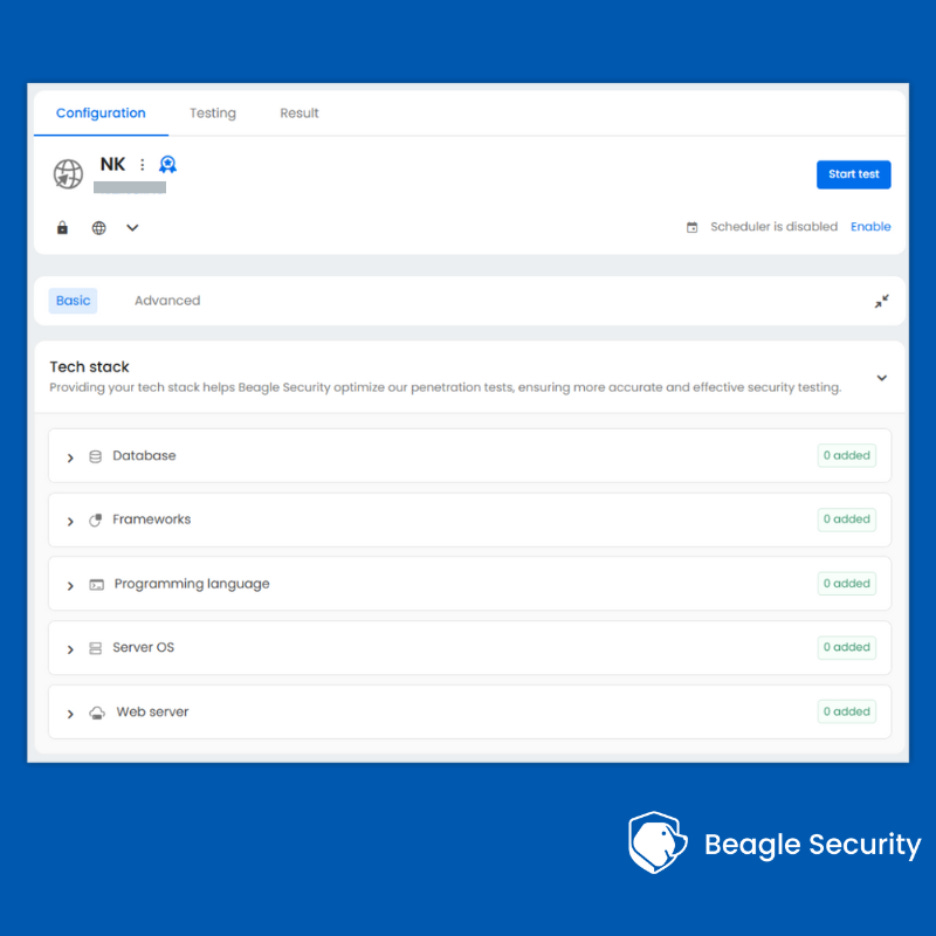
Tech-stack aware test case selection
Instead of running the same scans everywhere, our engine tailors tests based on your architecture, frameworks, and integrations. A Node.js API is tested differently than a WordPress app.
Business logic testing
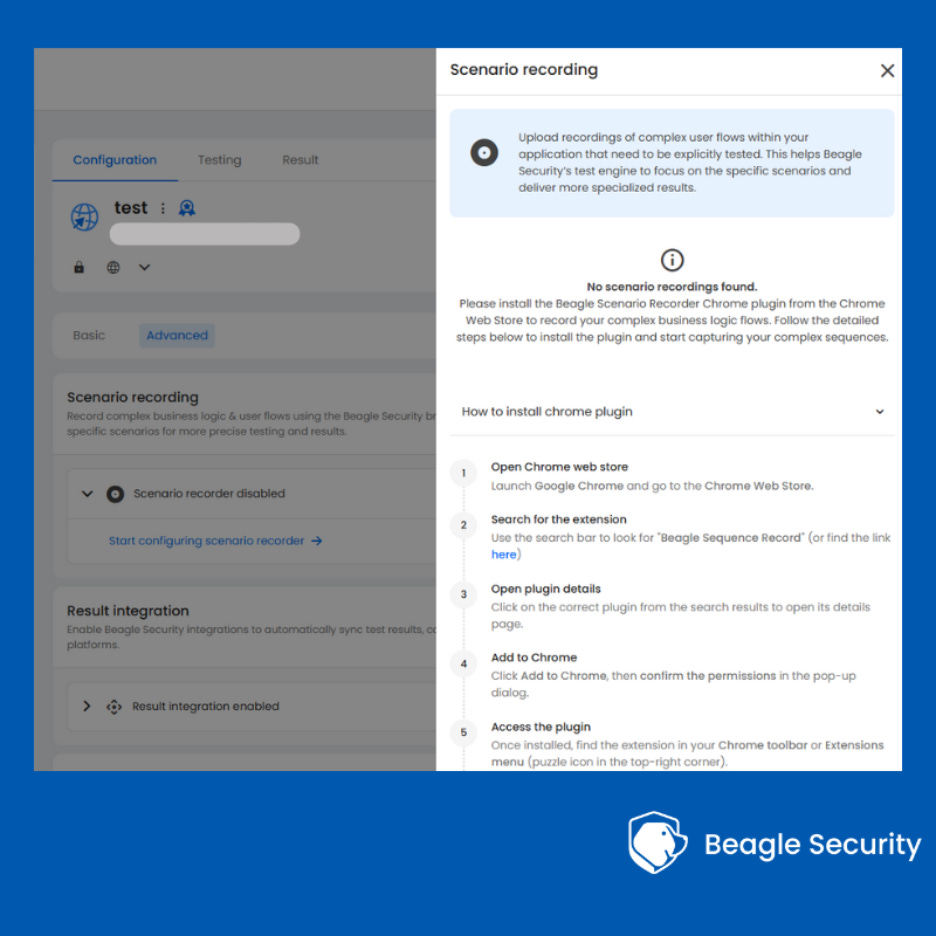
Using AI, Beagle Security simulates complex workflows and misuse cases that often slip past scanners. Users can also upload recordings of complex flows within their app that'll help Beagle Security's AI engine double down on vulnerabilities that may arise here.
Contextual reporting
Our reports highlight not just the “what” but the “so what.” You see which vulnerabilities could realistically compromise your data, your workflows, and your compliance posture.
The goal: security testing that reflects your real-world risks, not a generic checklist.
What you can do today
Even if you’re not using Beagle Secuity yet, here are practical steps to bring more context into your pentesting program:
Integrate threat modeling into every pentest
Make it a standard to start with your business processes and data flows.
Prioritize based on business impact, not just severity
Ask: “If exploited, what would this mean for us?”
Collaborate across teams
Involve product managers, developers, and security teams in scoping. They know where the sensitive flows are.
Revisit findings in your own environment
Don’t just rely on the pentest report. Map each issue to your assets and usage patterns.
Wrapping up
Attackers don’t care about CVSS scores or compliance checkboxes. They care about impact. And unless your pentests reflect that, you’ll always be playing catch-up.
The future of pentesting isn’t more scans. It’s smarter, context-driven security.
Because in AppSec, as in everything else: context is everything.